(Photo credit: Yuri Samoilov via Flickr Creative Commons)
You might not have realized it, but on October 21, 2016, the role of the CMO — and writ larger, business itself — changed forever.
Last Friday’s DDoS attacks on the Dyn Managed DNS infrastructure took out much of the Internet across North America. Twitter, Netflix, Reddit, AirBnB, SoundCloud, Spotify, Shopify, PayPal, GitHub, Disqus, Vox Media, Etsy, Time, and PlayStation were all affected. So was Amazon Web Services (AWS), which is used by more than one million businesses including GE, Capitol One, NewsCorp, Slack, Dow Jones, and many others.
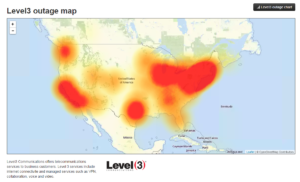
Image: Level 3 Outage Map/Down Detector)
This DDoS attack was different than those that have come before for two reasons. First, it didn’t target one company directly; it was a coordinated attack on a DNS hub. (If you’re not familiar with DNS or don’t understand how it works, there’s a good primer here.) DNS is how a web address is directed to a specific computer — like the old telephone switchboards, with a modern twist. This attacked flooded key DNS servers which made it difficult for many users to navigate or convert web domain names to the specific computers, leaving many in a state of flux, The perpetrators of the attack knew the key DNS servers to hit to have the broadest impact.
The second reason this attack was different was its clever use of the Internet of Things (IoT) to generate the DNS traffic necessary to take down Dyn. All those internet-enabled devices we have that make life convenient — from smart thermostats to DVRs, from refrigerators to the home security cameras we monitor from our smartphones — have an IP address. Those IP addresses were used to generate the traffic that flooded Dyn. It’s true: your DVR helped take down the internet Friday.
WELCOME TO THE FRONT LINES OF THE NEW WAR
We’ll ignore the rest of the details around security for a moment, for the purposes of this post. Your IT and security teams are putting plenty of thought into it right now, we assure you. The details are important, but the implications are even greater — and as a Chief Marketing Officer or senior marketing executive, you need to be aware of these implications.
First of all, we should have no delusions that this kind of broader, more widespread, IoT-based attack is going to happen again. There are already signs noted by security experts that someone (or lots of someones) is learning from attacks like this and learning how to take down the Internet.
Additionally, we can observe that attacks on the Internet have become weapons in the arsenal of many global players, from alleged Russian hacks of the American electoral process to Chinese and Russian hacks of western businesses, to Iranian efforts to hack everything from banks to dams in suburban New York, to the apparent state-sponsored attack on Yahoo that was only recently reported.. And those are just the state actors; hacking activity carried out by rogue groups or individuals pursuing various agendas have attacked companies from Target to Home Depot to Ashley Madison to TJX (parent company of TJ Maxx), among many others.
In previous global conflicts, wars were fought and casualties accumulated by militaries or those civilians unfortunate enough to be caught in the front lines; while business has certainly been impacted by war, it has never been on the front lines.
That has now changed forever. Like it or not, western businesses from the Fortune 500 to mom and pop shops are on the front lines of 21st century international conflict. It is no longer a question of whether your business might be impacted by hacks and other cybersecurity issues; it is a question of when.
THIS IS NOT JUST AN I.T. ISSUE; YOU ARE INVOLVED
These attacks are not merely the concern of your IT department and your corporate security team. Every aspect of your business can and will be impacted, and you should be preparing with a level of urgency with your plans to respond to these cybersecurity challenges.
One of the hallmarks of digital transformation (and largely of a 21st century business) is that every aspect of your business utilizes digital technologies and interconnectedness to improve efficiencies, simplify the customer experience, and control costs.
Your supply chain at this point most likely could be drastically impacted by breaches or attacks like the one we saw Friday. Should a DDoS attack on a DNS hub extend beyond one 24 hour period and be sustained for days or even weeks, what would the impact be on your supply chain? How might your suppliers be affected? Would things be delivered where they’re supposed to be? Would the right suppliers get paid? Could orders be placed or processed?
What about your customer experience? The impact of a data breach on your customers is obvious, but how would they be impacted by a coordinated and sustained attack that slows or takes down the internet (or at least the part of it that your sites reside on)? How would your business respond if your customers can’t get to your website, can’t use your mobile app, can’t connect to your digital customer service channels?
THE CMO’s JOB INCLUDES TECHNOLOGY
Historically, marketing and communications have never really been involved in security issues unless or until there is a problem. As of this week, this a short-sighted approach destined to cause reputation problems. Failure to understand and prepare for security issues is failure as a CMO.
If a data breach occurs, it affects the company’s reputation of course, and there is customer communication that has to happen around the security of their data. But too often, we either don’t think enough about this possibility or we place an overabundance of faith in our IT and security teams, and assume it won’t happen to us. Should a data breach hit your company, would you be improvising your communications and marketing response strategy? If your department hasn’t developed a strategy for the eventuality of a data breach — from communicating your security responses in a way that eases some customers’ concerns and shows decisive action without telegraphing too much to malevolent actors who might be still eyeing you — you’ve failed not just your customers but your employers.
What about a coordinated and sustained attack on the infrastructure that doesn’t directly target you, but renders your digital operations unusable for a period of time — like the one we experienced Friday? What would your communications strategy be? What would you say to consumers and customers, and how would you communicate to them? What might be the long term effects on customer confidence in your security — how would you adjust your marketing to address those concerns and mitigate that damage? Have you planned for a response to an indirect attack that takes you offline? Why not?
WHAT YOU SHOULD DO
Here are steps we recommend that every CMO take to prepare themselves and their companies for 21st century reality:
1) Understand that it’s going to happen to you. Prepare your plan for when, not if — because it’s only a matter of time before a breach or attack affects your company.
2) The CMO must make it a point to understand the technological basics of how the internet works. For too many of us, the Internet is just a platform; we have no deeper understanding of how it actually works than we have of the workings of the internal combustion engine that likely brought us to work. This is a mistake.
Do you, as the CMO, understand what a DNS server is and how it works? Learn. Do you know what BIND software is and understand its role? Or are you still thinking about it as just the famed mysterious series of tubes? The technical details of how the Internet works are not just someone else’s concern; they are yours. In a crisis situation, you will be glad you invested the time in learning the details so that you’re not left confused or flustered as your IT and security teams try to explain to you what has happened and why/how it’s happening. Make it your business to understand the way the Internet works.
3) The CMO should sit down with the CIO, CTO, or security and business consultants now — not after a problem occurs — to talk about the company’s specific digital security processes, procedures, and policies. Do you understand what a firewall is, how your company’s firewall works? Do you understand NAT and how your company uses it? Don’t just content yourself with understanding how the Internet at large works; make sure you understand how your company’s IT and security teams have implemented security processes and features at your business.
4) Talk candidly with the IT and security teams about what keeps them up at night — where your company might be vulnerable to breaches and attacks. This is for two reasons: first, so you become more familiar with the kinds of security challenges you may most likely be faced with; and second, so that you might become a more effective advocate inside company leadership for improved security and increased investment. Also, talk in advance about what details you can safely share with the public in a post-attack communication, versus which details might expose the company to further attacks or liability. You’ll want to know what you can say as well as what you shouldn’t.
5) Talk with the IT and security teams about areas that might represent a weakness that could be exploited. Do you sell IoT devices or products? How could these be impacted? Is there anything in the services you provide your customers — from online bill pay to remote access to their home, vehicle, or place of business — that could be used in an attack like this against the larger internet? How does the IoT and the Internet in general play in your supply chain and logistics, in your customer service and customer experience, in your employees’ connectivity, in your CRM and customer retention programs? What might be done to tighten security and insure the organization a little more against cyberattacks and data breaches? Understand these opportunities and advocate for them — you’re not carrying the CIO’s water, you’re protecting your company’s reputation.
6) Recognize that breaches and attacks will impact your company’s reputation — even indirect attacks. Develop a communications plan for both the immediate situation of a security incident and the long-term reputation recovery play you’ll need to run. Do this for every scenario the IT and security teams spell out for you. In the context of cybersecurity issues, failing to plan is planning to fail. How will you discuss events like Friday’s attack where maybe certain consumers were unable to reach your website through no fault of your own or security risk within your own properties?
7) Run crisis simulations or exercises with your team regularly. Many companies execute crisis simulations for their communications and marketing teams — everything from product failures to recalls to violent incidents at a workplace. Add data breaches and cyberattacks to this list, and run the team through the paces. Identify failings and gaps before you have to deal with them in real time.
Twenty-first century reality dictates that security is everybody’s business inside an organization — but it has especially become a marketing issue. It is a marketing executive’s responsibility to understand it, prepare for attacks and breaches, and advocate for fixes and upgrades to the company’s cybersecurity as a marketing and reputation issue.